OPENING THE UFO BORDERS
By:
Steve Erdmann
Copyright, C, Steve Erdmann and Alternate Perception Magazine
This article was previously published in the March 2019 issue of Alternate Perceptions Magazine.
http://www.apmagazine.info/index.php?option=com_content&view=article&id=1279&Itemid=194
It is published here again with permission.
Reviewers and journalists can quote small portions along with the full credits.
Another version of this article can be seen at The Borders are Now Open – https://wordpresscom507.wordpress.com/2020/06/07/
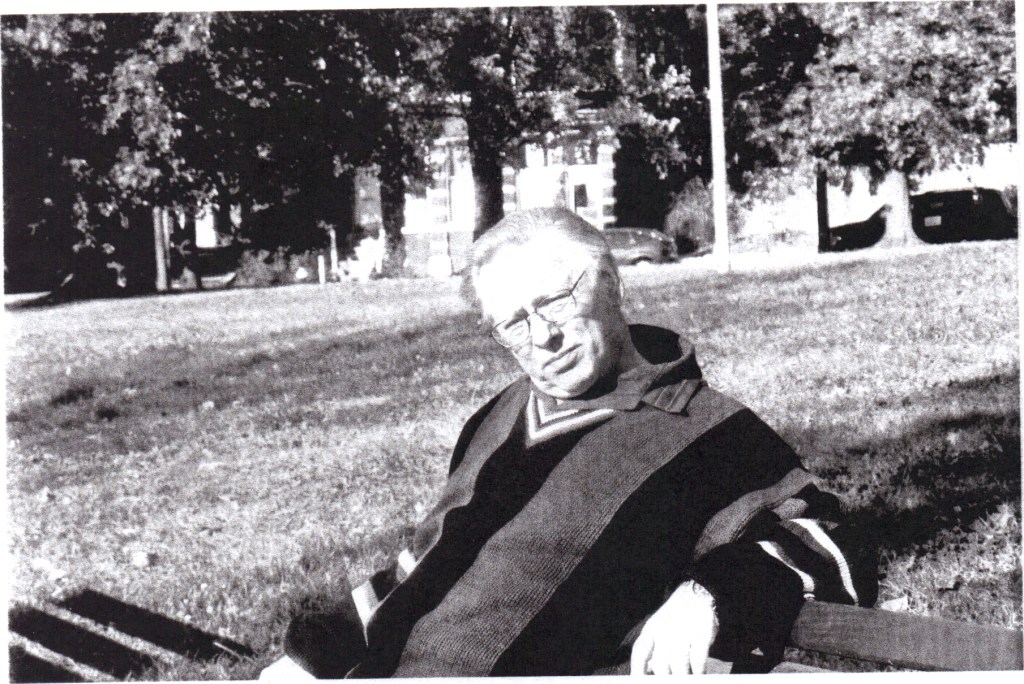
“Brent Raynes has been investigating and researching UFOs since 1967. He is the author of Visitors from Hidden Realms and the editor of Alternate Perceptions Magazine. Brent has traveled extensively across the US and into Canada interviewing numerous witnesses and researchers. He has taken a comprehensive global and historical perspective on the Ufological landscape. He has also participated in Native American rituals and ceremonies, gaining valuable insights and information from his interactions with these wisdom keepers. Brent is able to make revealing comparisons between the interrelated experiences and disciplines of parapsychology, shamanism, Jungian archetypes, and ufology.”
Brent Raynes – Paranormalist
**********

*****

Brent Raynes and wife.
Descriptions of UFOs seem as varied as do descriptions of the “science” that supposedly investigates them, but everything that pertains to UFOs is suddenly also in flux and question. The fifteen authors that have contributed essays in this book on the problematic situations and solutions to the aerial mystery agree strongly on one thing: New and radical changes to the modes of investigation need to come about.
(UFOs: REFRAMING THE DEBATE, edited by Robbie Graham, White Crow Books, 3 Hova Villas Hove, BN 33DH, United Kingdom; http://www.whitecrowbooks; info@whitecrowbooksa.com; 2017, 262 pages, $17.99.)

“Arthur C. Clarke once wrote that any sufficiently advanced technology would be indistinguishable from magic,” says Red Pill Junkie. “Perhaps he forgot to consider how any sufficiently advanced mentality would equally be indistinguishable from madness. In the search for the other by which to gauge our own self, what we’re really hoping for is a mirror depiction of our own expectations only slightly ahead of us such that it may still be comprehensible. Yet a truly alien mind would be from our own earthly perspective, and by the definition of the word, crazy…carnivalesque hall of mirrors….” (p. 152, italics added)
Red Pill Junkie sees comparisons to the “Joker” in batman and the Dark Knight movies and other Trickster Phenomena such as Indrid Cold of the tales of the 1960s Mothman flap.

Physicist Dr. Harley Rutledge discusses the 1973 Piedmont, Missouri UFO Flap
http://inthefield2017.weebly.com/dr-harley-rutledge—a-ufo-blueprint-to-follow.html
Progressing truly into the UFO Matrix takes both guts and creativity, says Lorin Cutts: “Within the UFO and paranormal experiences, there does appear to be some kind of an external intelligence interacting with us in a variety of ways. Yet, for obvious reasons, the nonsense and Trickster elements are all too often overlooked. Certainly building any kind of literal belief system round the UFO contact experience would – to say the very least – appear hugely problematic” (p.79).
By ignoring or negating the parapsychological aspect of UFOs, large portions of science are muted as puzzle pieces. There is no doubt that the UFO Mystery is “multi-casual” and needs to be approached differently.
“Currently, the testimonies of UFO witnesses that describe corresponding high-strange and paranormal events are often ignored or met with ridicule,” says Susan Demeter – St. Clair, “from ufologists who rather not deal with the more bizarre aspects of UFO reports, and the professional skeptic organizations who are open to anything other than the Null hypothesis…in my opinion, is a big mistake.” (p. 169)
COLLECTIVE SOCIAL REALITY
The fifteen essayists “leave no stone upturned.” M.J. Banias says the problem is much larger than any physical “Silence Group.” It is deeply ideological.
“There is no secret society that has imprisoned UFO discourse; rather, it is our collective social reality, governed by the mechanisms of modern capitalist ideology, that has done so…Today, science is no longer counter-cultured, but is now the arbiter of mainstream culture, the self-proclaimed hub by which all knowledge is. Ironically, science has become what it rebelled against.” (pp. 133, 135)

M . J Banias.
MJ Banias is an educator, writer and blogger. He was a former field investigator with the Mutual UFO Network, has been featured on multiple podcasts and radio shows, and contributes to Mysterious Universe and RoguePlanet. His work has been included in Fortean Times, FATE Magazine, and in a book entitled UFOs: Reframing the Debate. He is the author of The UFO People: A Curious Culture. He lives in Canada with his wife, two children, and a massive cat. To learn more, visit:www.TerraObscura.net.
https://www.youtube.com/watch?v=DbNA-8cNl2Q .
Banias talks about some of the prevailing elements “distorting” amateurs that affect ufology: Corporate influence is one, and the “ideological constructs” which our present society operates under, is another.
“We have given ‘science’ a sort of anthropomorphic consciousness,” says Banias, “but science is not a literal ‘thing,’ rather, it is a collection of socially accepted ideological constructs, methods and mechanisms, financially controlled by economic and political forces…various established organizations…a wide range of agendas.” (p. 137)
Smiles Lewis suggests there is a real “ParaCryptoufology” phenomenon that exists and is seen through a Gaian consciousness, but, at the same time, is being manipulated by covert earth agencies for their own hidden purposes.

A Smiling “Indrid Cold” Haunting Cases in the 1960s
https://www.historicmysteries.com/indrid-cold/
“This is the problem I have with most people who claim to have an answer to the UFO phenomenon. They pick a theory, but it only fits part of the data,” says Lewis. “That’s also why I advocate for a multi-theory interpretation of the UFO phenomenon. I don’t think there is any one explanation that accounts for all the data; in fact, many of the ideas I’m going to talk about would provide the perfect cover for such traditional extraterrestrial encounters.” (p. 110)
The end result of such an ‘alliance’ with the UFO denizens and earthly agencies could be seen in the “psychotronic mind-influencing techniques” connected to a “Cyber-biological-Planetary Poltergeist” in ways similarly to which science-fiction foresaw as a worldwide phenomenon of “earth energies” that evil minds about the globe have “hijacked by human agencies for nefarious purposes.”
“It is clear that quite a wide variety of human agencies have manipulated the superstition and myths surrounding stories of contact with non-human entities – folklore has been weaponized as a means to various ends,” says Lewis, and Lewis spreads a wide blanket of information in his essay (p. 127).
.

The ”Joker” as a Fatalistic Component
https://kotaku.com/gotham-city-s-newest-joker-is-an-eighteen-year-old-kid-1755484213
.
People are waiting for some kind of “disclosure” or “physical evidence” that will prove the reality of UFOs. Micah Hanks offers more definitive “categorization” of the phenomenon, adding many additions such as “experimental aircraft,” “drones,” “psychological components,” and several others.
“Obviously, science and, more importantly, the scientific method, rest at the cusp of what I seek to address in the present missive,” says Hanks. “Hence, in pointing out the adoption of a scientific ‘scientism’ amidst the modern skeptic movement is not to detract from the proper application of science by any means…perhaps more answers than we have managed to attain previously.” (p. 74)
Joshua Cutchin says that to approach the subject as to whether UFOs are nothing but nuts and bolts extraterrestrial space ships (N & B/ETH) would be a mistake:
“While plenty of cases superficially support the N & B/ETH view, its materialist foundations are shaken when confronted with the High Strangeness characteristics of a majority of UFO Close Encounters,” says Cutchin. “Alleged ‘alien’ abductees report profound synchronicities manifesting in their lives, battle poltergeist phenomenon in their homes, and occasionally encounter loved ones during their brief sojourn to the Other World.” (p. 51)
.

Joshua Cutchin – Researcher
https://www.joshuacutchin.com/single-post/2018/03/06/Render-Unto-Caesar-Possible-Alternative-Motivations-Behind-Government-UFO-Bigfoot-Secrecy
Cutchin’s astute essay pinpoints many over-looked areas, and especially how “materialistic science” is a fading science being divorced by current evidences of psychic phenomena in a growingly “brick-by-brick” paradigm. Cutchin notes multiple studies by scientists such as Rupert Sheldrake, Daryl Bem, Ian Stevenson, Pim Van Lommel, Alex Tsakiris, and a ‘slew’ of others that say a new world of “psi acceptance domino chains” will eventually rewrite the “rule book” and finally explain many UFO episodes (pp. 55-59).
Researchers, such as Lorin Cutts, go further and say that “almost everything you think you know about flying saucers is wrong.”
“We should start to study all aspects of non-standard human experience together,” says Cutts. “We can no long continue to treat the UFO phenomena as separate from other paranormal, spiritual, religious, esoteric, highly synchronistic or other currently uncategorized phenomena. Whether we utilize science or also include other methodologies and philosophies, one thing is certain: we need to stop trying to fit that UFO subject into what we want or expect it to be.” (p. 87)
Cutts blasts “current scientific understanding” as a societal “paper god” that just can’t presently confront in-coming “magical, high strangeness” and experiences that “mystify and confuse!” New pathways and new escape routes, says Cutts, are needed (pp. 89-90).
In his own personal experiences Mike Clelland sees UFOs and related phenomena as a “confusing collision of over lapping experiences, a mess of twists and turns,” as the various threads of “synchronicity spill over to the edges.”
Researchers tend to look upon the UFOs in tight, tidy visions about visiting space ships, says Clelland, but “it’s equally important to look beyond the physical clues…We are dealing with a phenomenon that can seep its way into our reality in ways that are both outlandish and profound.” (pp. 28-30).
In a distorted, vain, and miscalculated, search for “respectability” and the “perfect case,” says Greg Bishop, “we have backed ourselves into a corner” by routinely ignoring the “fields of psychology, physiology, and even the emerging discipline of information theory” which should be included (pp. 189-191).
“Can we get ourselves out of the equation to see the phenomenon for what it really is, if there is such a thing?” Adds Bishop, “If there is a non-human consciousness interacting with us, occasionally, there is probably no way to see them except in relation to us.” (p. 205)
UFO stories come to us out of every culture, says Bishop, in the symbols of “dragons, phoenixes, pearls, holy spirits, saints, giant tanks, honey-combed spider-webbed ships, glowing orbs, triangles with red lights, and football field-sized platforms that block out whole chunks of the sky.” (p. 211)

https://en.wikipedia.org/wiki/The_Shadow
.Methods of investigation have been “haphazard,” “quite harmful,” and witness stories have exploded into “an orgy of squabbles over belief systems, and the wringing of hands over the imminence of government Disclosure.” (ibid)
There are many fundamental problems and influences that have “distorted” ufology from its beginning, says Jack Brewer, ranging from deceptive opportunists to “charlatans,” (p. 42) to “involvement in the intelligence community” (p. 39), including “the long-arm of the CIA and its UFO-related interest.” (p. 38)
“To reframe the debate, effectively, and competently, we must not only acknowledge that such dynamics are happening,” says Brewer, “but make consistent decisions to swim against the undertow and be more of the solution than the problem.”
Brewer suggests better “methods” that will allow researchers to get to the “heart” of the phenomenon: “We would be wise to drop preconceived notions to the best of our abilities.” (p. 47)
LOOK BEYOND STRUCTURES
Ryan Sprague says that now is the time for an “expansion of awareness” and move past the mentality we are dealing solely with “nuts and bolts” and “physical analysis” and seek “newly-disclosed perception” which stretches the limits of our perceptional reality.
“It may be that our established modes of logic limit us so greatly that we can’t fully comprehend the monster we created,” says Sprague. “We must ultimately face the fact that, at some point, the awareness of that monster is going to shape and mold our consciousness completely, moving forward.”
https://www.somewhereintheskies.com/
Smiles Lewis sees different “origins” of the UFO phenomena in the style of the “Controllers,” “agent provocateurs,” and governmental suspects that are fond of using “psychotronic mind control devices” in “the lens of covert-ops and deception” (pp. 121-122). MK-Ultra, Project Blue Bird, Project Monarch, Rand Projects, and others that very well have been realized in certain UFO cases such as classical episodes of The Flatwoods Monster of 1952, the Antonio Vilas Boas case of 1957, Barney and Betty Hill case of 1961, and several others of this semblance.
.

https://www.thewindowsclub.com/nsa-prism-icms-big-brother
.
But a real phenomenon exists beneath the human nefariousness and shenanigans, says Lewis, and has connected somewhere along the line of activity as a “cyber-biological planetary poltergeist.” Lewis highlights The Excalibur Briefing by Thomas Bearden:
“He, too, describes the onion-like aspect of the collective unconscious or the Akashic records and this idea that we could be interacting through these phenomena,” says Lewis, “through the transpersonal channel that I’ve been trying to describe here – with various aspects of our own individual unconscious, the collective unconscious of the entire species or, as he breaks if down, to family, city, state, creed, nations, race, geographical area, species, biosphere, and the universal.” (p. 116)
Lorin Cutts points to the Yakima, Washington UFO “hot spot” as a classical case-in-point. Like so many other “hot spots,” there is a need to utilize cutting-edge technology such as super-high resolution cameras. But Cutts suggest the bigger mystery would be to “measure” the human experience with emphasis on the interaction with the subconscious mind (p. 87).
When Joshua Cutchin speaks on such “elements,” he is reminded of magician Aleister Crowley’s 1918 summation of an entity called “Lam,” a typical Grey alien, asking us to “move beyond materialism” towards a “non-dogmatic Gnosticism.”
.

Aleister Crowley’s Depiction of “Lam”
“…the materialist paradigm will fall apart given time,” says Cutchin, “and consciousness studies are the proverbial star…” (pp. 61-62)
Sunday, March 10, 2013 was Mike Clelland’s “Confirmation Event.” When returning from a UFO conference, Clelland and a friend decided to camp along the Utah roadside. Later, he awoke to see a giant round structure on top of a nearby hill that appeared to have a ring of lights around it. He observed it about an hour, assuming it was a large home.
Clelland went back to that exact spot where the “home” should have existed: nothing was there. Clelland did find that three unusual or paranormal events fell along a 231- mile-long-straight line, including a ‘point’ where one of the events had previously occurred outside of Dolores, Colorado in the Spring of 2010, reminiscent of Aime Michel’s Flying Saucers and the Straight Line Mystery.
http://www.ignaciodarnaude.com/ufologia/Maney,A.Michel%20Straight%20Lines,FSR59V5N6.pdf
“Synchronicities, more psychic flashes, number sequences, and coyotes,” says Clelland, “all play a part in this frenetic narrative…it’s not just one isolated event; it’s a lot of them…” (pp. 20-21)
Robert Brandstetter recounts a UFO experience in 1977 that happened to him and a friend outside an ice rink in Northern Ontario. “…two classic illuminated and seemingly metallic ships descend…” within the distance of telephone pole height. Multi-colored lights were around the perimeter. They were completely silent. One object went back to join its partner UFO after passing over a neighborhood house; there were many witnesses. The two objects ascended at an incredible speed and faded into the stars (pp. 222-223).
Brandstetter claims several extraordinary experiences; one such happening was in 2005 when he observed an object in the sky while he was meditating while walking in the woods, the environment seemed to change about him, “transforming the woods into a surreal aquatic phantasmagoria” resulting in the meeting of a “strange woman.”
Greg Bishop relates four UFO incidents that do not match comfortably “into a standard narrative.” One case involved Jerry Townsend of Long Prairie, Minnesota which on October 23, 1965 sighted a 40-foot “rocket” standing on three ‘fins’ in the middle of the road. Three small figures that looked like “beer cans on two legs” waddled over to him and balanced themselves on a third leg. They soon disappeared back into the “rocket” which then took off with a “humming” sound, disappearing in the sky.
.

http://inexplicata.blogspot.com/2012/08/machines-from-elsewhere-robots-and-ufos.html
THE UFO CRUX IS PERSONAL
The more “traditional stances” to the UFO question (at least those who seem to hold tinges of old-fashioned skepticism) can be seen in the essays of Curt Collins and Chris Rutkowski. Rutkowski believes that “proper science” is being contaminated by overbearing “UFO zealots” who distort the field and are actually a fantastical “religion” that needs to be ‘negated’ to a separate track of inquiry and apart all together (p. 15).
Curt Collins examines the November 2013 Roswell Slides case of a purported body of a photographed, retrieved small alien. A Roswell Slides Research Group was formed and it was composed of numerous skeptics, cynics, even debunkers and some other professional people who diligently investigated the slides as a Task Force, eventually discovering the photos to be an earthly mummified body of a two-year-old boy (pp. 106-108).
Rutkowski denotes the need for finding hard, cold facts; Collins stresses this also along with good ‘teamwork.’ The conundrum, however, is: What if this does not encompass ‘all’ the evidence and information, and what if it is guided by faulty, fundamental logic and methods that are not attached to the ‘latest’ philosophy and reason?
Greg Bishop says there are other ways to look at this. “We labor under this heavy legacy, but it does not have to be so,” says Bishop. “A conscious effort should be made not to assign any origin or meaning to these encounters, because we may have been fooling ourselves for so long about what they are that we have backed ourselves into a corner.”
The fields of psychology, physiology, and also “information theory,” even Pyrrhonism, are needed (pp. 191-192).
Ryan Sprague concludes that “new paths” depend on up-coming UFOlogists. Despite their scientific grounding or their metaphysical knowledge, they must give us their time, knowledge, and resources to live with a “foot in each camp.”
“We must look beyond the structures we’ve helped create,” Sprague stresses again, “and bring life to a monster we want neither to destroy nor resurrect ever again. We must let it live on its own terms and in its own image.” (p.187)
Other literature:

“Jacques Vallée, one of the first to research the covert manipulation of the UFO scenario by official agencies, concluded: ‘someone is going to an awful lot of trouble to convince the world that we are threatened by beings from outer space.’ But how does this fit in with his Magonian hypothesis? Vallée presented his most explicit statement of the big picture in the story-line of his 1996 novel Fastwalker (written with Tracy Tormé): a powerful group of human conspirators know that the UFO phenomenon is created by entities from a parallel world, but they aim to convince world leaders and the global population of the existence of ‘aliens’ – and then position themselves as the world’s go-betweens.
“Which is basically our own view of the case of the Council of Nine: they have the stamp of the Ultraterrestrial all over them – clowns, conmen and cosmic jokers – but there is also the pernicious presence of very human agencies lurking in the background. The joke is on all those who follow the Ultraterrestrials, however they choose to manifest themselves or however their human allies choose to present them to us. But, as history has shown, it may be no laughing matter.”
Quotes from the below article:
https://www.newdawnmagazine.com/articles/behind-the-mask-aliens-or-cosmic-jokers
*******
Steve Erdmann, February, 2019, St. Louis
*******
.
You can reach Steve Erdmann – at – dissenterdisinter@yahoo.com – or – independenterdmann@gmail.com.
His Facebook email is http://facebook.com/stephen.erdmann1.
You can friend him at:
Facebook – https://www.facebook.com/stephen.erdmann1 –
Or – visit the Dissenter/Disinter Group – https://www.facebook.com/#!/groups/171577496293504/.
His Facebook email is http://facebook.com/stephen.erdmann1.
You can also visit his articles at the following:
mewe.com/i/stephenerdmann1,
http://www.minds.com – TheDissenter,
http://www.ufospotlightwordpress.com,
http://www.ufodigestblog.wordpress.com,
http://www.ufodigest.com,
Alternate Perception Magazine: http://www.apmagazine.info/.

Steve Erdmann – Independent Investigative Journalist
*******
Another version of this article can be seen at The Borders are Now Open – https://wordpresscom507.wordpress.com/2020/06/07/




























































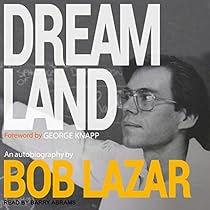
 Bob Lazar
Bob Lazar









 Robert Morningstar & Dr. Bruce Maccabee at the National Press Club with USAF Colonel Charles Halt (background left) at Leslie Kean’s Generals, Pilots, and Government Officials’ UFO Press Conference Washington, DC – Nov. 12, 2007
Robert Morningstar & Dr. Bruce Maccabee at the National Press Club with USAF Colonel Charles Halt (background left) at Leslie Kean’s Generals, Pilots, and Government Officials’ UFO Press Conference Washington, DC – Nov. 12, 2007

